About the Data
The CSS dataset is dedicated to SMTP traffic, only listing port-25 based detections. Potential triggers for a listing include unsolicited emails, having poor email marketing list hygiene, or sending out malicious emails due to compromised accounts or content management systems (CMS). Both IPv4 (/32) and IPv6 (/64) addresses are listed in the CSS.
Policy statement
The Spamhaus CSS list is an automatically produced dataset of IP addresses that are involved in sending low-reputation email. CSS mostly targets static spam emitters that are not covered in the Policy Blocklist (PBL) or Exploits Blocklist (XBL), such as snowshoe spam operations, but may also include other senders that display a risk to our users, such as compromised hosts.
Benefits of this data
Based on a wide range of inputs, and always the result of multiple events and heuristics, this subset of the Spamhaus Blocklist normally contains between 2 and 4 million listings, with 300,000 to 400,000 new listings added every 24 hours.
Email administrators can apply this real time DNSBL to reduce the overflow of inbound email traffic associated with spam and other malicious emails. Gain industry-leading catch rates with extremely low false positives to reduce risk of security incidents, reduce email infrastructure costs, and reduce human resource requirements.
How to utilize this dataset
To make the best use of Spamhaus' data, blocklists should be utilized at specific points during the email filtering process.
For the CSS, it is included in the Spamhaus Blocklist zone, as a subset of SBL, and should be used during:
- The initial connection – against the connecting IP.
- Once the email data has been accepted, by checking IP addresses in the Received chain in the mail headers, and by looking up IP addresses hosting resources appearing in the body - such as URLs.
For more information on this, read this best practice.
Get more protection, for free
Each blocklist targets a specific type of behavior; using one blocklist independently limits the effectiveness of the data. Spamhaus offers three other IP-based blocklists for free:
These IP blocklists can be used via ZEN which combines the above datasets for easier and faster querying.
The majority of malicious email is dropped at the SMTP transaction, however many bad actors invest time and money to evade IP-detection. So to gain the best catch rates, domain and hash blocklists should also be used to filter email, once the email has been accepted. For this, Spamhaus provides the Domain Blocklist (DBL) for free. Find more on why you should use domain and hash blocklists here.
Technical information
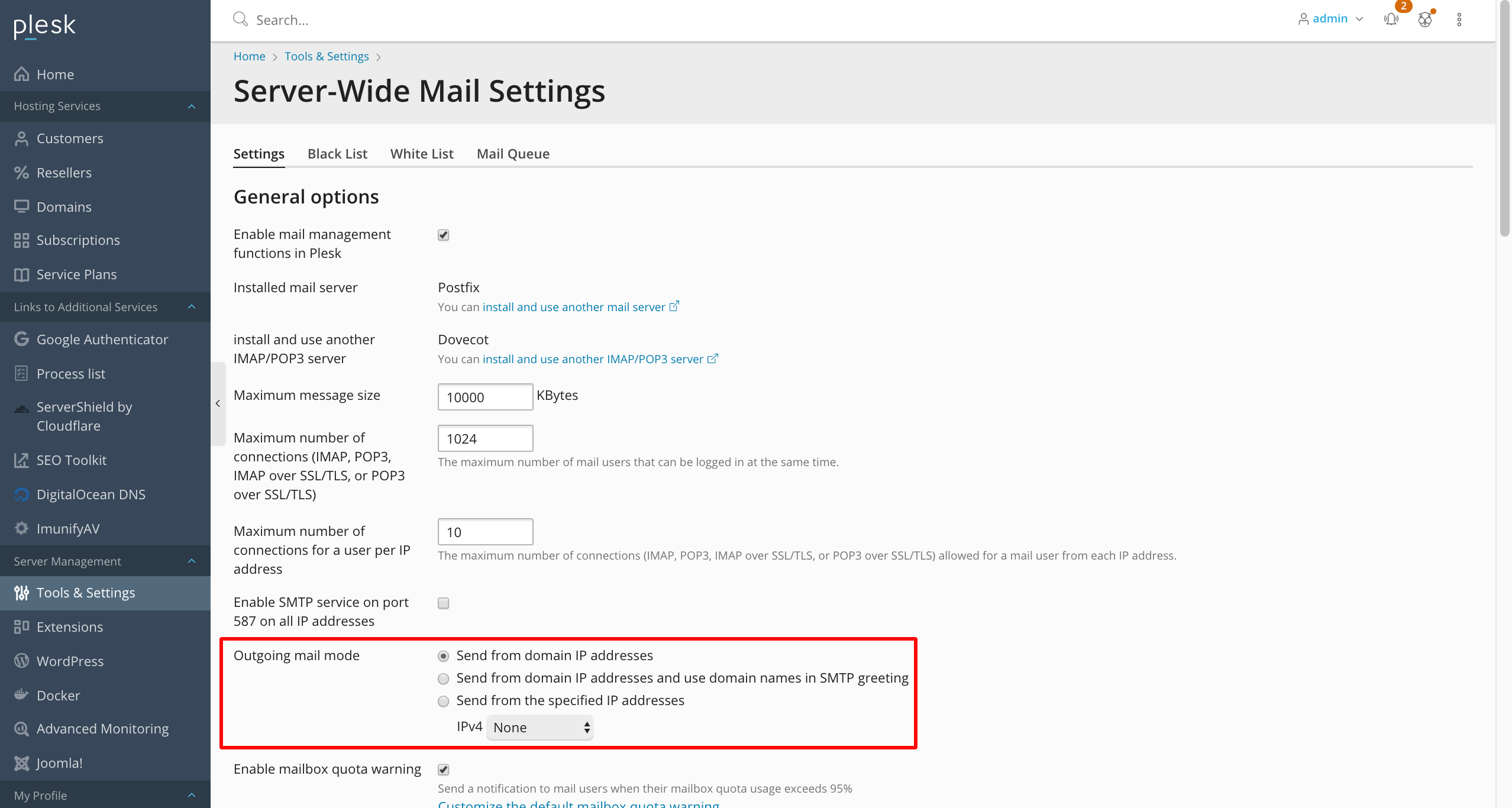
You can utilize the data via the SMTP server configuration for connection and SMTP transaction checks, and via open source tools, such as SpamAssassin and Rspamd, for content analysis.
Downloadable plugins for SpamAssasin and Rspamd are readily available to minimize configuration time, for users of Spamhaus Technology's real-time DNS Blocklists.
Alternatively, integrate with your existing anti-spam platforms with technical information to support here. Set up takes minutes and you instantly gain real time protection.
Accessing the data
Use of the Spamhaus DNSBLs is free of charge for low-volume, non-commercial users. If you’re unsure, please check our DNSBL usage criteria. Free accounts are made available through our partner, Spamhaus Technology - sign up to access the data via the free real-time DNS Blocklists.
Where data is being used for commercial purposes, an annual subscription-based service is required. Sign up for a free 30-day trial.
Best practices to maintain a positive IP reputation
Spamhaus’ data protects billions of mailboxes globally. To avoid getting listed and your email service being impacted, some important best practices are:
- IP warm up - when bringing on new IPs, slowly ramp up the amount of mail being sent. This is where reputation begins to be established and so is a critical step.
- Proactive configuration - before using new IPs, ensure that they are configured properly at least 30 days before the first send.
- Restrict outbound SMTP traffic - configure your firewall to allow outbound SMTP traffic (destination port 25) only if originated from your mail server internal IP (if you have one).
- Infrastructure - check your internet infrastructure providers, e.g. ISPs. See reputation statistics on ISPs/networks.
- Use double opt-in – to avoid spam traps and ensure only real and interested recipients are sent your emails.
- Configuration – ensure that your hostname and your HELO match, and that your reverse DNS (PTR record) is defined and pointing to the same hostname.
N.B. We recognize these are not all managed by email administrators; where applicable, communicating with other functions, like network administrators and deliverability specialists, is critical.
Removal
If your IP is listed on the CSS blocklist, you should visit https://check.spamhaus.org. This will take you to our IP and Domain Reputation Checker for more information, and the only place where CSS removals are handled.